Is Your Boss a Snoop
It's for Your Own Good!Information on the Internet is subject to the same rules and regulations as conversation at a bar. - Dr George Lundberg ...the Internet may fairly be regarded as a never-ending worldwide conversation. - Stewart Dalzell My favourite thing about the Internet is that you get to go into the private world of real creeps - Penn Jillett Website for Complaints Sparks Lawsuitby Charles Odum Dallas, Georgia - When Alan and Linda Townsend were unhappy with the sprayed-on siding applied to their house, the frustrated couple launched a website to complain and to give other unsatisfied customers a forum. Visitor postings to the website said the product, Spray on Siding, cracked, bubbled and buckled. For their efforts, the Townsends got slapped with a lawsuit by the product's maker. The federal case may help shape the boundaries of online speech. Companies routinely go after individuals when they feel people are maligning them on the Internet. And often, legal scholars say, the website's owners don't fight back at all. In this dispute, North Carolina-based Alvis Coatings Incorporated, which supplied the siding product used in the Townsends' $16,721 project, claims the couple's website infringes on the company's trademarks, defames its product and intentionally misleads and confuses consumers. Alvis is seeking more than $75,000 in damages in addition to unspecified punitive damages and attorney fees. "We could lose everything, including the house, and still be in debt," said Alan Townsend, whose house is valued at around $150,000. Though neither side was looking for a brawl over speech rights, the lawsuit is headed that way, said Paul Levy, an attorney for Public Citizen, which agreed to help represent the Townsends. Internet law expert Doug Isenberg of Georgia State University said the courts need to better define free-speech issues for the Internet, and this case could help. "The right to criticise is certainly protected in general, but it is not unlimited," Isenberg said. "Some of those limits include how you can use someone else's trademark." The complaint filed by Alvis alleges that the name of the Townsends' website, spraysiding.com, "is confusingly similar" to the official Alvis site, sprayonsiding.com, as well as its trademark "Spray on Siding." Levy argues that the Townsends have the right to use the domain name they purchased. Courts have provided greater protection to non-commercial sites, such as the Townsends', "but it is not quite so cut-and-dry to say if it is non-commercial use it's acceptable," Isenberg said. Judges also weigh whether a person is likely to confuse the gripe site with the real one, said Wendy Seltzer, staff attorney with the Electronic Frontier Foundation, a San Francisco-based civil-liberties group. A site that bashes a product is not likely to create such confusion, she said. Companies have threatened scores of criticism sites with trademark infringement and have lost many of the cases that have actually gone to court, Seltzer said. But most of the time, she said, the site owners simply agree to stop before a lawsuit is even filed. Thus, the boundaries of their rights are never tested. Having this case and others like it go to court should help better define permissible conduct - and perhaps discourage companies from such threats in the future, if they know they would likely lose, Seltzer said. The Townsends' website has a message board in which other customers comment. Alvis' lawsuit, filed in September in US District Court in Charlotte, North Carolina, contends the Townsends are responsible for posting the "false, misleading and disparaging" comments on that message board. A federal law offers some protections to Internet providers for content their visitors post or transmit, and courts have separately held that criticism when framed as opinion is not libelous, legal scholars say. But like the trademark challenges, many website owners don't bother fighting in such cases, said Deirdre K Mulligan, director of the law and technology clinic at the University of California at Berkeley. Craig Hartman, Alvis's chief operations manager, said his company sued the Townsends only after months of fruitless dealings with the couple. "We truly want the people who use our product to be satisfied," Hartman said. Hartman said the company made three "formal generous offers" to the Townsends that were rejected. He said the lawsuit was a last resort. The Townsends say one settlement offer from Alvis included a gag order barring them talking about the product and a demand that the couple sell their site's domain name to the company. They decided they would rather fight so that other potential customers could be better informed about the product. "As long as this stuff is on our house, we're going to talk about it," Linda Townsend said. "You could say we're very idealistic about this." Charles Odum is a writer for Associated Press Source: story.news.yahoo.com Saturday 6 November 2004
Online Laundry: Government Posts Enron's E-Mail
A personal email written to an Enron employee by Dennis K Berman Amid Power-Market Minutiae, Many Personal Notes RemainLike so many office workers, people at Enron Corporation made company email an extension of their personal lives. They used it for romance, they used it to complain, they used it to arrange funerals. Now, because of an investigation of the fallen energy company, a lot of those private exchanges are on the Internet for all to see. A little browsing and up pops a piece of email from an Enron employee complaining about a mother-in-law: "the most selfish person on Earth." Another contains decades-old photos of former chief executive Jeffrey K Skilling, sent him by his Beta Theta Pi fraternity brothers. A piece of email written by a woman in Portland, Oregon, asks an Enron energy trader, "So ... you were looking for a one night stand after all...?" The Federal Energy Regulatory Commission gathered a massive trove from Enron in its investigation of alleged energy-market manipulation. In March the agency released more than 1.6 million pieces of email and other documents and posted them all on the web in a searchable database (www.ferc.gov). The emails roughly cover the years 2000 through 2002. At no charge, viewers can troll through the email boxes and calendars of 176 current and former Enron executives and employees, most of them involved in the company's power-trading operations. The names of the emails' senders and recipients are still attached. "This job is absolutely crazy," wrote one lawyer working in the Enron Gas Pipeline Group in May 2000. "If you ever watch 'ER,' that is usually what my day looks like, only without all the blood." A number of well-known names make database appearances. In an August 2000 email titled "Kennebunkport and other," the president of Texas Southern University, Priscilla Slade, invited former Enron chairman Kenneth Lay to a weekend hosted by former President Bush. Mr Skilling was sent invitations to golfing events with US House Majority Leader Tom DeLay and MCI Chief Executive Michael Capellas - then head of Compaq Computer Corporation. People still working at Enron found their dirty laundry on display, not to mention some of their bank records and their Social Security numbers. Enron employees call such personal exposure abusive and an invasion of their privacy. "There was no reason why Enron turned [the emails] over in the first place, and why FERC decided to make them public, other than that California politicians wanted to punish Enron," says 56-year-old Teb Lokey, who recently retired after more than 29 years handling regulatory matters at Enron. Mr Lokey was sitting at his desk on the 39th floor of Enron's Houston headquarters in March when word started spreading about the database. He typed in his name and "was just shocked," he says. There were "something like 7,000 or 8,000 documents with my name on them," he says. Other Enron employees tapped into the database to see what their bosses were saying about them, or to try to take a peek at a colleague's salary. The database is supposed to help the public better understand whether Enron helped to create - and then profit from - an energy shortage in California during 2000 and 2001, according to FERC. The database is therefore loaded with lots of technical emails between power traders, discussing "price curves" and "hub contracts." FERC spokesman Kevin Cadden says the agency gave Enron sufficient notice - three weeks - that it would be releasing the data collected for its investigation but that Enron didn't respond. Speaking of the sensitive personal information, Mr Cadden says, "I don't think that people want it there, and I don't blame them. But Enron is the owner of the documents and they had an obligation to tell us what is personal information. It did not do so." Enron spokesman Mark Palmer says the company has "cooperated with FERC's investigation and will continue to cooperate. We have asked them to protect innocent employees' personal records." Two days after the email was posted online, Enron petitioned FERC to get some of it removed, particularly Social Security numbers. The agency agreed to remove a few of the most sensitive emails, including a payroll document that listed the Social Security number of every employee, says a person familiar with the investigation. Nonetheless, employees began to stumble across all kinds of other material and inundated an Enron hotline with angry messages asking that certain documents be removed. Following a US Court of Appeals order in early April, the database was disabled for 10 days, during which time Enron was allowed to identify every email it wanted removed. About 100 employee volunteers, mainly from the company's human-resources department, sat down at their PCs to slog through hundreds of thousands of messages. Each volunteer was given a chunk of files to search, looking for such terms as "Social Security number," "credit card number" and "divorce." The company gave raffle prizes - Houston Astros tickets and Enron T-shirts - to those who did the most searching. The grand prize was a day off. Over dinners of pizza and fajitas, the search team grew more expert at finding personal email. The keyword "kids," for instance, was especially effective at tracking down information about children that didn't really belong in the database. But there were also judgment calls about whether some private email conversations were personally harmful enough to be stricken from the public record. For instance, the search teams had to decide whether discussions of someone's birthday plans might be dangerous if a name and birthdate got into the hands of an identity thief. FERC eventually removed about 8% of the database, or 141,379 documents. But Enron employees continue to believe that too much personal material remains on public view. As of 8 August, FERC had spent 350 hours reviewing about 17,185 of the documents for which confidentiality had been requested. Of those, only 5,128 are being withheld permanently, the FERC said. Those are mainly documents containing Social Security numbers and employee performance evaluations. Still available on the site are the emailed photographs of a college-age Mr Skilling taken by fraternity brothers at Southern Methodist University. In one, he is seen squinting from behind his horn-rimmed glasses, tightly gripping the lapels of his jacket. The correspondence mentions his fraternity nickname, "Rocky." An attorney for Mr Skilling didn't return calls requesting comment. Plenty of reminders of personal distress remain online, such as one October 2000 email between onetime co-workers, in which one writes, "I just thought something needed to be said about Wednesday. We could just go on and act like nothing happened and probably never see or talk to one another ever again. I don't like that solution." For many of the Enron employees, the database has become a lesson in the do's and don'ts of email. A former employee who asked not to be named said, "I think before I send anything on email now. If I need to talk about something personal, the email will say, 'Call me when you have a minute.' " Dennis K Berman is a staff reporter for the WSJ; write to him at dennis.berman@wsj.com Source: The Wall Street Journal 6 October 2003
Internet Publishers Caught in Legal Webby Denis Dutton
Email and the web have abolished forever the tyranny of distance over New Zealand's access to global information. This is a remarkable benefit of a communication system originally designed by the American military to have so many alternative interconnections that it could survive nuclear war. When we go online in New Zealand we also have access to exactly the same newspapers and magazines available elsewhere. At least until now. A disturbing Australian legal decision last month could change that. Joe Gutnick, a colorful multimillionaire Australian goldmining magnate (and rabbi), sued Dow Jones, publisher of the Wall Street Journal and Barrons, for defamation. Barrons had carried an article alleging he had been involved in money laundering and tax evasion. Everyone agrees that Rabbi Gutnick deserves his day in court. The crucial question is, which court? Will it be the Supreme Court in Melbourne, where Australian defamation laws give him a reasonable chance of winning, or an American court, where free-speech legal traditions built around the First Amendment of the United States Constitution would make success unlikely? The High Court of Australia unanimously decided last month that Rabbi Gutnick may sue in Victoria, rather than the US, since it is in Victoria that his reputation was harmed. For any internet publisher, it's an alarming decision. The worldwide web is exactly that: interlocking connections that go everywhere from any place. There are perhaps 190 countries on the internet, presenting a crazy-quilt pattern of penalties for such crimes as libel, blasphemy against the state religion, or criticising the country's rulers. The Australian decision would in principle require any publisher with worldwide interests to water down the content of websites to be in accord with 190 different legal systems. Anything that breaks local laws criticising Islam, perhaps, or some backward country's president for life could on this Australian reasoning open the publisher to suits. If the publisher is a news organisation with local assets, such as an office building, these could be forfeit, even if a judgment were unenforceable in the publisher's home country. One of the Australian judges, Justice Callinan, said: "Publishers are not obliged to publish on the internet. If the potential reach is uncontrollable then the greater the need to exercise care in publication." He also expressed the view that Dow Jones was attempting to impose on Australians an American legal hegemony in relation to internet publications. But before Australians start cheering the victory of local defamation laws over hegemonic, alien notions of free speech, they ought to think hard about who the real losers from this decision will be. Consider the following scenario. If the Gutnick decision stands, Dow Jones can follow either of two strategies: first, it can have its articles and opinion pieces dealing with Australian companies and businessmen vetted by Australian lawyers before publication in order to fit Australian defamation law. This would be awkward and very expensive. Alternatively, Dow Jones can continue its practice of robust reporting of Australian business, but do its best to block internet access into Australian jurisdictions, so it is not seen as intentionally publishing in Australia. It would make much better sense for Dow Jones to follow this second path, offering information which is protected by the First Amendment in the US to its American readers, and to other readers around the globe where it is legal to do so. But now, if you are an Australian investor, you will face an unsettling, potentially disastrous situation. Suppose Dow Jones, which is after all the most important business and financial information source in the world, uncovers dirt about some Australian tycoon that would incline investors to dump shares in the tycoon's company. Dow Jones will send the information (via an email alert or a Wall Street Journal article) worldwide except to Australia, where the story might be actionable. Thanks to the Gutnick decision, American investors could then sell their shares first, probably to Australian investors who have been saved from the hegemony of American law and American free speech by Justice Callinan and his colleagues. Scenarios like this give us an appreciation of why the likes of Thomas Jefferson and John Adams insisted on freedom of speech as the first principle to be ratified as an amendment to the new US Constitution. Too bad the High Court of Australia does not see it that way. It wants to have it both ways: Australians should be able to sue for defamation on strict Australian criteria but also enjoy freedom of speech as guaranteed by the US Constitution and made available on the internet. It won't wash. The Gutnick decision will be welcomed by dictators everywhere. Already in the last year, Zimbabwe set a nasty precedent by arresting a journalist whose crime was to write an article that was not published in Zimbabwe but could be downloaded in that sad land. Robert Mugabe can rightly regard the Gutnick decision as validating his state censorship. Meanwhile, moving in exactly the opposite direction, a US court ruled last month that a resident of Virginia could not sue for defamation in her home state when the offending article was posted on the internet by a Connecticut newspaper. The Pentagon's original aim to create an information system that could survive nuclear attack was successful. But not even the computer geniuses of the Pentagon could devise a system to survive the onslaught of lawyers and judges. If these censors have their way in Australia and elsewhere, we will all be losers. The Gutnick decision must not stand. And if it does, it must not be imported into New Zealand law. Denis Dutton teaches in the department of philosophy at Canterbury University. Source: nzherald.co.nz New Zealand Herald (a great newspaper, folks) 7 January 2003
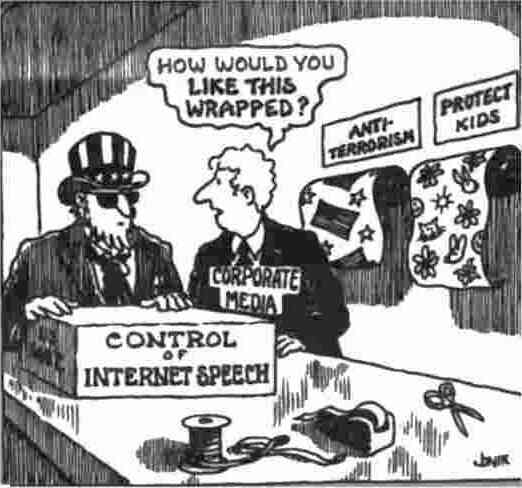
Other Countries Can Add "Defamation"...
Source: Funny Times August 2000
Technical Warby Ted Bridis Washington - The government's pursuit of terrorists is relying heavily on sophisticated technology, from software that automatically translates foreign communications on the Internet to a device that secretly captures every keystroke a suspect makes on his computer. President Bush signed new anti-terrorism legislation Friday that enabled law enforcement to rely on these tools more freely, and the Justice Department immediately sent instructions to prosecutors. "A new era in America's fight against terrorism ... is about to begin," Attorney General John Ashcroft pledged. Over the weekend, top Justice lawyers in Washington emailed the most cyber-savvy federal prosecutors around the country, describing in more than 30 printed pages how they can use the government's high-tech tools in new ways. The email, reviewed by The Associated Press, outlines new guidelines, for example, for operating the FBI's Carnivore computers, which capture suspects' emails in ways that require only perfunctory approval by a judge. Another section says that in rare cases police can now secretly search a person's house without telling the homeowner for up to three months. During one of these so-called "sneak and peek" searches, authorities would secretly implant a hidden "key-logger" device. The FBI acknowledged making five such secret searches before it installed its snooping device in a recent gambling investigation. The key-logger, hidden inside a computer, secretly records everything a suspect types on it. The device lets authorities capture passwords to unscramble data files in otherwise unbreakable codes. Bush said this weekend that new anti-terrorism laws were needed because modern terrorists "operate by highly sophisticated methods and technologies." (The US government has its own share of gee-whiz gadgetry - enough for a season of Mission: Impossible.) The CIA is rushing to teach its computers how to better translate Arabic under a young program it calls "Fluent." Custom-written software scours foreign Web sites and displays information in English back to analysts. The program already understands at least nine languages, including Russian, French and Japanese. Another CIA breakthrough is "Oasis," technology that listens to worldwide television and radio broadcasts and transcribes detailed reports for analysts. Oasis currently misinterprets about one in every five words and has difficulty recognising colloquial Arabic, but the system is improving, said Larry Fairchild, head of the CIA's year-old Office of Advanced Information Technology. In a demonstration earlier this year at CIA headquarters, Fairchild showed early plans for "CIA Live!," which lets CIA experts send instant messages and collaborate on reports and maps across the agency's ultra-secure computer networks. The FBI and police in Boston and Miami are using powerful software called "dTective" from Ocean Systems Company of Burtonsville, Maryland to trace financial transactions linked to last month's terrorist attacks against New York and Washington. The software, which runs on highly specialised, $25,000 equipment from Avid Technology Incorporated, dramatically improves grainy video from surveillance cameras at banks or automated teller machines. It can enhance images, for example, that were nearly unusable because of bad lighting. "Sometimes we're amazed at the quality of the image," said Dorothy Stout, a top specialist at Veridian Corporation in Oakton, Virginia, who teaches police how to use the video system. Other tools help her rebuild videotapes that have been burned, cut into pieces or thrown into a lake. "It's quite time-consuming," she said. At US computer-crime labs, including a cutting-edge Defense Department facility near Baltimore, technicians rebuild smashed disk drives from computers. They also use sophisticated commercial software, called "Encase," which can recover deleted computer files and search for incriminating documents on a seized computer. Experts are hard at work in the FBI's headquarters in Washington, using Encase and other tools to examine computers seized after the 11 September attacks. Source: dailynews.yahoo.com from the Associated Press
FBI Retires Its Carnivoreby Kevin Poulsen [Excerpt] FBI surveillance experts have put their once-controversial Carnivore Internet surveillance tool out to pasture, preferring instead to use commercial products to eavesdrop on network traffic... The FBI didn't use Carnivore, or its rebranded version "DCS-1000," at all during the 2002 and 2003 fiscal years. Instead, the bureau turned to unnamed commercially-available products to conduct Internet surveillance ... in criminal investigations in that period. Carnivore became a hot topic among civil libertarians ... in 2000, when an ISP's legal challenge brought the surveillance tool's existence to light. One controversy revolved around the FBI's legally-murky use of the device to obtain e-mail headers and other information without a wiretap warrant - an issue Congress resolved by explicitly legalising the practice in the 2001 USA Patriot Act. Under section 216 of the act, the FBI can conduct ... Internet surveillance without first visiting a judge and establishing probable cause that the target has committed a crime. In such cases the FBI is authorised to capture routing information like e-mail addresses or IP addresses, but not the contents of the communications. Source: securityfocus.com 14 January 2005
Still Free to Believe
Source: Funny Times - Huck/Konopacki Labor Cartoons Aug 2K solidarity.com
What's More Important?London - Britain is braced for legal war over how far employers can snoop on their staff in the digital age. Other Western countries watch closely. A new business-friendly law effective today will spark a struggle over intercepting communications and just how private an email or a phone call at work can be. Bitchy remarks, job enquiries, union activism, details of illness or a secret sex life - people say or write things they'd hate their boss to know. The new law, the next round in perhaps a long fight, gives bosses wide monitoring powers. The crux of the issue is whether workers have the right to expect privacy if they use a work phone or email connection. In one corner are businesses, who say they need wide access to staff communications to do their job properly, to answer business mail sent to a worker who is ill, to control telephone help lines or to check for computer viruses. On their side is the new act of Lawful Business Practices Regulations, whose initial monitoring restrictions were loosened after companies complained they would create an intolerable burden. Originally businesses would've needed consent from both parties to a phone call or email before intercepting it. "A secretary would've been acting illegally if she checked her boss's emails without gaining the sender's consent too," said employment lawyer James Davies. In the other corner are the unions and anti-surveillance campaigners, who say the new law ignores any right to privacy. "I would't expect someone to force open my filing cabinet if I'm off sick with the flu," said Chris Evans of the anti-regulation pressure group, Internet Freedom. This camp won round two earlier this month when the official Data Protection Commissioner said in a code of practice that employees' rights to privacy were being undermined. The draft code laid down strict rules for electronic monitoring and said a worker had a right to a degree of trust and to work "without constantly being watched." The code will also have the status of law, causing confusion and bringing a bumper harvest for lawyers as courts are asked to decide which law is the real one. "The Regulations will carry more weight, but the data commissioner has the back-up of the Human Rights act," said Richard Arthur, a human rights lawyer. The European Human Rights act became law in Britain at the beginning of October, and unions said their members might invoke it to fight what they see as unacceptable Orwellian spying in the workplace. "We're unhappy that employers might trawl through emails routinely," said a spokeswoman for the Trades Union Congress (TUC). "In the hands of the wrong employer, this could be dangerous." It's unclear whom the new law permits to monitor, read or record communications. It says the "system-controller" is in charge but can delegate authority. Another murky area is how close a tab can be kept on an individual's Internet surfing habits, although some things, such as downloading pornography, are banned almost everywhere. What both camps agree on is that the issue is now in a muddle. "We all need to sit down and agree a way forward," said the TUC spokeswoman. The law is a delayed part of a controversial recent bill that gives Britain stronger surveillance powers than other Western states, which must themselves address the issue soon. The Regulation of Investigatory Powers act obliges Internet service providers to install listening posts if requested so that police or intelligence services can monitor email traffic. The state says this is the only way to combat organised crime and racist or other hate groups. Business with private telecoms systems have until now been at liberty to intercept communications as they wish. Current legislation was written in 1985 before the advent of email and the widespread use of private communications networks. While most people would have had private post sent to their home or marked clearly "private and confidential", emails are different, as many people have no home Internet access. A private email will still be private under the new law. But an employer will have the right to read down to find out if it is a business or private matter. "It is rarely obvious from the heading of an email whether or not it contains business information," said Rod Armitage, head of legal affairs for the Confederation of British Industry. Once the boss recognises a message is private advice on how to deal with your HIV-positive status, for example, he or she must stop reading immediately, but the damage is done, critics say. Source: The Nation (Bangkok) 24 Oct 2000
Just Making Sure We Can Trust You
Source: Funny Times October 2000
The Chef's Surpriseby Jim Hightower It's the paranoid's worst fear: They really are watching you. We've learned in recent years that privacy is passe in practically every aspect of our lives as corporate and governmental snoops track our movements at work, in schools, walking down the street, browsing on the Internet...and now, even while we eat. The New York Times reports that some of the city's finest restaurants have installed cameras to monitor your meal. You wouldn't notice, unless you happen to look up at the ceiling, where a small camera lens is peering down at you, conveying the image back to a screen in the kitchen. New digital surveillance cameras provide remarkably clear pictures of your dining habits, and they have zoom lenses that can capture such close-up details as what you're writing on a cheque. They also allow "remote access," meaning a chef away from the restaurant can tune into the dining room through a computer...and watch you eat. [And listen to what you say?] The rationale is that these peek-a-boo systems allow chefs to know when you're finishing your appetiser so the entree can arrive on time. But, the cameras also pick up your intimacies, including if you and your date get a little smoochy, providing voyeuristic fun for the kitchen staff. Also, if the chef can catch the action online, so can any 12-year-old computer whiz who wants to take a peek around the tables. In addition to the cameras, the Times reports that more and more restaurants are building personal profiles on their customers, compiling databases that include your phone number, address, profession, eating preferences, how much you drink, et cetera. Again, this nosy bit of data collection is done in the name of efficiency and meeting customers' desires - but the bottom line is that your intimate dining experiences are being watched, recorded, stored, and used without your permission. This digital prying gives new meaning to the term "chef's surprise." The hell with efficiency - give me some privacy! Source: Funny Times October 2000
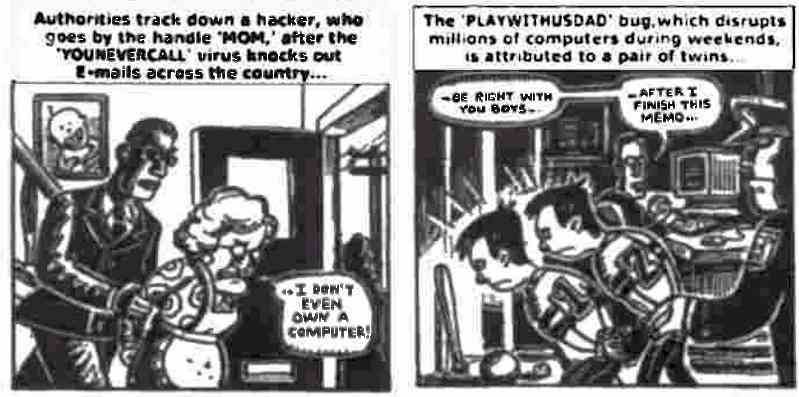
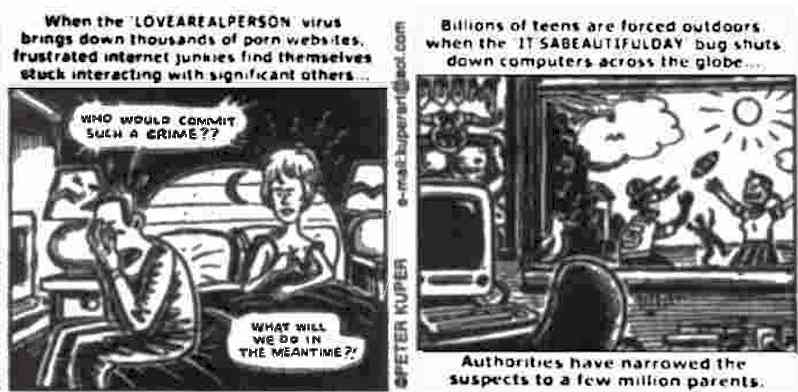
Is Anything Important?by Peter Kuper As our world gets totally wired to computers, the threat of more bugs like the "I LOVE YOU" virus is inevitable...
Source: Funny Times September 2000
Intel's FingerprintsSuppose there was a device on your car that came on every time you started up and then broadcast a signal identifying you wherever you drove. You could turn it off, but it would start up again automatically the next time you started the car. Would that be a violation of your privacy? Most people would probably think so - and a similar proposal in cyberspace resulted in a storm of controversy this week, when Intel Corp. first announced, and then retreated from, a plan to create a unique hard-wired "fingerprint" from each of the chips it makes for personal computers. With the feature in place, it would be easy to track individual computers as they navigated through the Web, for example. Electronic vendors would know for sure what computer was making a purchase; your bank could tell for sure that the computer inquiring about your account balance was the same one you signed on with before. But privacy groups that objected to the chip ID plan announced an Intel boycott, complete with an ad campaign featuring "Big Brother inside" ads that spoof the "Intel inside" campaign the chip-maker runs. An influential congressman joined the criticism, and Intel quickly retreated from the plan. Now, instead of having chips that identify themselves unless told otherwise, the company is providing software that disables the feature unless a user specifically asks to turn it on. That may actually accomplish many of the original intentions of the feature, allowing positive identification when appropriate without forcing unsuspecting users to leave cyber-fingerprints when they didn't intend to. The rules of the road in cyberspace are still being sorted out. It's not surprising that controversies such as the Intel chip identification are arising. Users will need to be vigilant in making their wishes known as the technology matures. Source: © Nando Media and Scripps McClatchy Western Service; originally from The Sacramento Bee 28 January 1999 Also see:
For IT-related articles on snooping, usage, the future, e-diaries, piracy, flickers, cyborgs, browsing, trends, jokes, philosophic agents, artificial consciousness and more, press
the "Up" button below to take you to the Table of Contents for this Information and Technology section. |
 Animals
Animals Animation
Animation Art of Playing Cards
Art of Playing Cards Drugs
Drugs Education
Education Environment
Environment Flying
Flying History
History Humour
Humour Immigration
Immigration Info/Tech
Info/Tech Intellectual/Entertaining
Intellectual/Entertaining Lifestyles
Lifestyles Men
Men Money/Politics/Law
Money/Politics/Law New Jersey
New Jersey Odds and Oddities
Odds and Oddities Older & Under
Older & Under Photography
Photography Prisons
Prisons Relationships
Relationships Science
Science Social/Cultural
Social/Cultural Terrorism
Terrorism Wellington
Wellington Working
Working Zero Return Investment
Zero Return Investment
 The internet is rightly regarded as close to
miraculous in its capacity to provide immediate access to information and opinion worldwide. New Zealanders used to wait for weeks to
lay their hands on overseas newspapers. Now, we can fire up our computers on any afternoon and read the British newspapers hours
before Londoners have opened their paper copies over breakfast. By dinnertime, we can do the same with The New York Times and the Wall Street Journal.
The internet is rightly regarded as close to
miraculous in its capacity to provide immediate access to information and opinion worldwide. New Zealanders used to wait for weeks to
lay their hands on overseas newspapers. Now, we can fire up our computers on any afternoon and read the British newspapers hours
before Londoners have opened their paper copies over breakfast. By dinnertime, we can do the same with The New York Times and the Wall Street Journal.